Deep within the shadowy recesses of the internet lies a realm known as the dark web. A place shrouded in secrecy, where anonymity is paramount and identities remain untraceable. To access this clandestine world, one needs a specialized tool: onion links. These enigmatic addresses, constructed using multiple layers of encryption, serve as the portal to the dark web's hidden corners.
Each onion link acts as a unique pathway, leading to websites that operate outside the purview of conventional search engines and surveillance. Navigating this labyrinthine landscape requires caution and knowledge, as dangers lurk within its depths. From illegal marketplaces to confidential information, the dark web offers both allure and peril.
For those seeking anonymity or access to forbidden content, onion links provide a means. However, it's crucial to remember that venturing into this realm comes with inherent risks. Users must be vigilant about security measures and exercise utmost caution when interacting with the unknown.
Navigating the Labyrinth: A Guide to Onion Links
The shadowy realm of onion links can be a daunting trial for even the most seasoned internet explorer. These deeply layered connections, often found in the underworld of the web, offer a glimpse into a world removed from prying scrutiny. But navigating this labyrinth requires a careful and methodical approach.
- Initially understanding the onion link itself. It's a URL that ends in ".onion", signifying its connection to the Tor network, a system designed for anonymous surfing.
- Following this, acquire a secure and reliable Tor browser. This specialized software allows you to access onion links safely and privately.
- Be aware that not all onion links are created equal. Some may lead to legitimate resources, while others could be harmful. Exercise caution and always verify the reputation of a site before engaging with it.
Bear in mind that navigating onion links is a journey into the unknown. Proceed with preparedness and awareness for the potential risks involved.
Venturing into Realm of Onion Services
Onion Systems, often referred to as Invisible Networks, represent a fascinating layer of the internet. These layered networks operate on the I2P protocol, obscuring user identities and traffic from prying intruders. While portrayed as illicit activities, Onion Services also offer a range of legitimate uses, including privacy-focused communication and freedom of information.
- Navigating the Onion Services realm requires technical skills, but the potential rewards can be significant. From researching sensitive topics, Onion Services present a unique gateway to discovering alternative perspectives of the internet.
Exploring Into Onion Link Destinations
Navigating the obscure world of onion links can be a daunting experience. These deep web passages often lead to mysterious content, concealing everything from {underground{ forums to clandestine marketplaces. However, for the brave explorer, onion links offer a unique glimpse into alternative corners of the internet, where information flows openly.
- Discovering the layers of security that protect onion sites
- Charting the complex network of onion links
- Encountering communities and individuals within the onion layer
Although navigating this digital landscape requires caution, understanding how onion links work can provide valuable insights into the evolution of online privacy and the ever-changing nature of the internet.
Unmasking the Deep Web: A Guide to Onion Links
Venturing towards the dark corners of the internet, one encounters the enigmatic realm known as the deep web. Accessible only through special protocols, it conceals a vast of information, both benign and shadowy. A key to unlocking this veiled world are onion links, special sequences that point to sites situated on the Tor network.
- Constructing an onion link involves sophisticated procedures that encrypt the destination address, making it undetectable to conventional search engines.
- Exploring the deep web with onion links requires a specialized program like Tor, which routes your information through a series of computers worldwide, masking your true position.
Considering the potential benefits of accessing unavailable information, it's vital to proceed with caution. The deep web can also be a hazardous place, harboring illicit activities.
Navigating Onion Links Responsibly
Diving into the depths of onion links can be enticing, offering a glimpse into hidden corners of the onionlinks internet. However, this entry point comes with inherent risks. It's crucial to approach onion links carefully, understanding that they can lead to suspect content, malware, or even underworld dealings. By employing effective security measures, using reputable sources, and exercising judgment, you can reduce these risks and harness the potential benefits onion links offer. Remember, knowledge is power in this complex digital landscape.
- Prioritize strong antivirus and firewall protection.
- Implement a secure VPN to encrypt your connection.
- Exercise caution of suspicious links or downloads.
- Explore onion sites thoroughly before engaging.
- Stay informed about the latest security threats and best practices.
 Jaleel White Then & Now!
Jaleel White Then & Now!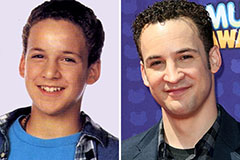 Ben Savage Then & Now!
Ben Savage Then & Now! Bug Hall Then & Now!
Bug Hall Then & Now! Jurnee Smollett Then & Now!
Jurnee Smollett Then & Now! Marcus Jordan Then & Now!
Marcus Jordan Then & Now!